The specter of the piper quinn leak 2026 looms massive, a hypothetical state of affairs that calls for cautious consideration. We’re stepping right into a future the place digital breaches will not be simply potential, however doubtlessly devastating, to dissect the potential repercussions of an information launch attributed to Piper Quinn. This is not simply concerning the technical features; it is a deep dive into the human factor, exploring the emotional, authorized, and reputational ramifications that would ripple by way of Quinn’s life and the broader digital panorama.
The investigation begins with the origins, the potential pathways by way of which Quinn’s non-public info may have been uncovered. We’ll delve into the technical methodologies employed by malicious actors, from refined hacking strategies to the extra refined artwork of social engineering. From there, we look at the authorized and moral quagmire, the potential for misinformation campaigns, and the preventative measures that would have, or ought to have, been in place.
This is not merely a thought experiment; it is a essential exploration of the vulnerabilities inherent in our more and more interconnected world and a reminder of the significance of digital safety.
Speculate on the potential origins of the alleged Piper Quinn leak within the 12 months 2026: Piper Quinn Leak 2026
The alleged Piper Quinn leak of 2026, a hypothetical occasion, presents a fancy state of affairs for digital safety evaluation. Understanding the potential origins of such a leak is essential for anticipating and mitigating future breaches. A number of vectors may have been exploited, highlighting the multifaceted nature of digital vulnerabilities. The next sections delve into the potential sources and strategies that would have led to the compromise of Piper Quinn’s info.
Attainable Sources of the Information Leak
The information attributed to Piper Quinn in 2026 may have originated from quite a lot of sources, every representing a definite level of weak spot in digital safety. These sources vary from compromised private units to vulnerabilities in cloud storage and insider threats. Understanding these potential origins is paramount to establishing efficient preventative measures.Compromised private units are a big entry level for knowledge breaches.
This contains smartphones, laptops, and good residence units. Malware, phishing assaults, and unsecured Wi-Fi networks can all be exploited to realize entry to a tool. For instance, a seemingly innocuous e-mail attachment may comprise ransomware, encrypting all knowledge and demanding a ransom for its launch. One other risk is the set up of spy ware, which covertly screens person exercise, capturing passwords, looking historical past, and delicate communications.
The proliferation of Web of Issues (IoT) units additionally widens the assault floor. Sensible fridges, thermostats, and different linked units typically have weak safety protocols, making them weak to hacking and knowledge theft. These units can be utilized as entry factors to a bigger community, permitting attackers to entry different units on the identical community. The assault floor has elevated considerably through the years, from primary net looking to complicated interconnected units.Cloud storage vulnerabilities pose one other vital threat.
The anticipation surrounding the Piper Quinn leak of 2026 continues to construct, with hypothesis operating rampant throughout varied on-line platforms. This fervor, nevertheless, just isn’t with out precedent; comparable eventualities have performed out earlier than, reminding us of the fragility of privateness, as seen within the latest case of drew gulliver leaked. In the end, the long run repercussions of the Piper Quinn leak in 2026 stay a topic of appreciable dialogue and debate.
Cloud companies are handy for knowledge storage and entry, however in addition they signify a concentrated goal for attackers. Information breaches can happen on account of vulnerabilities within the cloud supplier’s infrastructure, misconfigurations by customers, or compromised person accounts. As an example, a misconfigured storage bucket may expose delicate knowledge to the general public web, making it simply accessible to anybody. One other state of affairs includes a classy phishing marketing campaign concentrating on staff of a cloud supplier, having access to inside programs and doubtlessly exfiltrating huge quantities of knowledge.
Even with strong safety measures, cloud companies will not be resistant to assaults. A 2023 report revealed a big enhance in knowledge breaches on account of vulnerabilities in cloud configurations, demonstrating the continued risk.Insider threats, each malicious and unintentional, are one other vital supply of knowledge leaks. Malicious insiders could deliberately leak knowledge for monetary acquire, revenge, or different motives. Unintentional leaks can happen on account of negligence, corresponding to staff shedding a tool containing delicate info or inadvertently sharing knowledge with unauthorized people.
For instance, a disgruntled worker with entry to Piper Quinn’s knowledge may copy and promote it on the darkish net. Equally, a careless worker may go away a laptop computer containing delicate knowledge on public transport. Organizations should implement strict entry controls, common safety consciousness coaching, and knowledge loss prevention (DLP) measures to mitigate insider dangers. The frequency of insider threats highlights the significance of complete safety protocols.
Technical Strategies Employed within the Information Breach
Acquiring the Piper Quinn info in 2026 would doubtless contain a mix of refined technical strategies. Attackers would leverage varied strategies, together with social engineering, malware deployment, and direct hacking, to infiltrate programs and extract knowledge. The evolution of those strategies displays the fixed arms race between attackers and defenders within the digital panorama.Social engineering would doubtless play a vital position.
Attackers may use phishing emails or focused spear-phishing campaigns to trick people into revealing delicate info or putting in malware. For instance, an e-mail seemingly from a trusted supply, corresponding to a financial institution or a social media platform, may request a password reset or ask the recipient to click on on a malicious hyperlink. Profitable phishing campaigns typically contain meticulously crafted emails that mimic professional communications, making them troublesome to detect.
One other approach is “baiting,” the place attackers go away contaminated USB drives in public locations, hoping somebody will decide them up and insert them into their laptop. This technique exploits human curiosity and might result in the set up of malware.Malware deployment can be one other vital part of the assault. Attackers may use varied kinds of malware, corresponding to spy ware, ransomware, and trojans, to realize entry to Piper Quinn’s knowledge.
Spy ware could possibly be used to watch person exercise, seize passwords, and steal delicate info. Ransomware could possibly be used to encrypt knowledge and demand a ransom for its launch, creating vital disruption and potential monetary loss. Trojans, disguised as professional software program, may present attackers with distant entry to programs, permitting them to steal knowledge and set up further malware. For instance, a trojan is likely to be hidden inside a seemingly innocent software program replace, granting attackers full management over the compromised machine.Direct hacking strategies would doubtless be employed to use vulnerabilities in programs and networks.
This might contain exploiting software program vulnerabilities, corresponding to buffer overflows or SQL injection flaws, to realize unauthorized entry. Attackers may also use brute-force assaults to guess passwords or exploit weak safety configurations. For instance, an attacker may scan a community for open ports and recognized vulnerabilities, then use specialised instruments to use these weaknesses. One other approach is “man-in-the-middle” assaults, the place attackers intercept communication between two events to steal delicate info.
These assaults typically goal unencrypted or weakly encrypted communication channels.
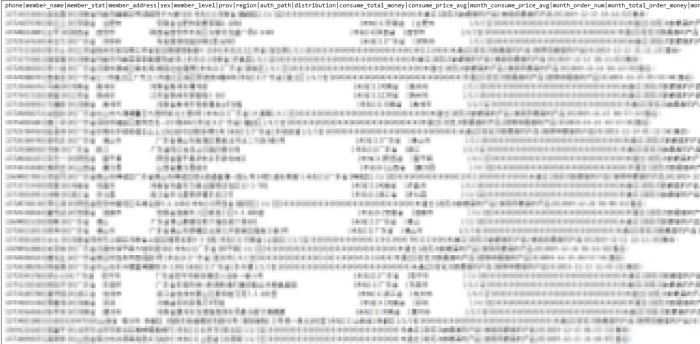
Kinds of Data Contained within the Leak
The information attributed to Piper Quinn may embody a variety of knowledge, various in sensitivity. The leaked knowledge may vary from extremely private info to much less delicate knowledge, doubtlessly revealing insights into varied features of her life and actions.
- Private Data: This is able to doubtless embrace personally identifiable info (PII) corresponding to title, deal with, date of beginning, social safety quantity, and get in touch with particulars. This knowledge is commonly focused by identification thieves and used for fraudulent actions.
- Monetary Information: Checking account particulars, bank card numbers, and transaction historical past could possibly be uncovered. This info is very beneficial to cybercriminals and can be utilized for monetary acquire.
- Communication Data: Emails, textual content messages, and social media conversations could possibly be leaked, revealing private relationships, opinions, and delicate discussions. This knowledge can be utilized for blackmail, reputational injury, or to collect additional intelligence.
- Medical Data: If Piper Quinn’s medical data had been compromised, they might embrace diagnoses, remedies, and different delicate well being info. This knowledge is protected by privateness laws and its publicity may result in critical penalties.
- Skilled Information: This might embrace work emails, confidential paperwork, and proprietary info. Such leaks can injury skilled reputations and result in authorized points.
- Geolocation Information: Details about Piper Quinn’s location, together with journey historical past and real-time location knowledge, could possibly be uncovered. This could possibly be derived from GPS knowledge from her units or from social media posts.
- Looking Historical past and On-line Exercise: Particulars about web sites visited, search queries, and on-line purchases could possibly be revealed, offering insights into her pursuits, habits, and preferences.
- Images and Movies: Private photographs and movies, together with these of a personal nature, could possibly be leaked. This could trigger vital emotional misery and injury private relationships.
- Social Media Information: Data from social media profiles, together with posts, likes, and connections, could possibly be uncovered, doubtlessly revealing her social circle and on-line conduct.
- Mental Property: If Piper Quinn is concerned in any artistic endeavors, corresponding to writing or music, her unpublished work could possibly be leaked. This might result in copyright infringement and lack of potential revenue.
Examine the potential authorized and moral implications stemming from the rumored Piper Quinn knowledge launch

The alleged launch of Piper Quinn’s knowledge in 2026 presents a fancy net of authorized and moral issues. This example necessitates a radical examination of potential ramifications for all events concerned, from these buying the info to these distributing it and, crucially, these whose private info is compromised. Understanding these implications is significant to mitigating injury and stopping comparable incidents sooner or later.
Potential Authorized Ramifications for Information Acquisition and Distribution
The unauthorized acquisition and distribution of private knowledge, corresponding to that doubtlessly concerned within the Piper Quinn leak, may set off a cascade of authorized actions. People concerned in both acquiring or disseminating the knowledge may face a large number of prices and lawsuits, the severity of which might depend upon the character of the info, the strategy of acquisition, and the intent behind its distribution.Civil lawsuits are nearly assured.
Affected people, together with Piper Quinn herself, may sue these answerable for the leak for invasion of privateness, negligence, and emotional misery. Damages sought in these instances may embrace monetary compensation for reputational hurt, misplaced revenue, and the prices related to mitigating the results of the info breach, corresponding to identification theft safety and credit score monitoring companies. For instance, think about the 2015 Ashley Madison knowledge breach.
The people whose knowledge was uncovered confronted comparable civil lawsuits, demonstrating the tangible influence of such incidents. Additional, the extent of legal responsibility will be fairly vital; the extra delicate the info, the upper the potential damages.Legal prices are additionally a definite risk. Relying on the jurisdiction and the precise legal guidelines violated, people may face prices associated to knowledge theft, laptop hacking, and the unauthorized entry of private info.
Legal guidelines such because the Laptop Fraud and Abuse Act (CFAA) in america could possibly be invoked if the info was obtained by way of unauthorized entry to laptop programs. Penalties for these offenses can vary from substantial fines to prolonged jail sentences. If the info leak concerned using malware or different malicious strategies, the severity of the fees and the potential penalties would enhance.
The actions of the perpetrators can be scrutinized, on the lookout for proof of intent to trigger hurt, monetary acquire, or some other type of malicious function.Moreover, firms or organizations that performed a task within the knowledge breach may face regulatory investigations and penalties. This might embrace fines from knowledge safety authorities, such because the Basic Information Safety Regulation (GDPR) in Europe, which has the ability to levy vital fines on organizations that fail to guard person knowledge adequately.
This underscores the significance of sturdy knowledge safety measures and the intense authorized penalties of failing to implement them.
Framework for Evaluating Moral Concerns, Piper quinn leak 2026
The Piper Quinn knowledge leak necessitates a radical moral analysis, shifting past mere authorized compliance. This analysis should heart on the privateness rights of people and the potential for reputational injury, alongside contemplating the broader societal influence of such occasions. A complete framework ought to deal with a number of key areas.The cornerstone of the moral evaluation is the respect for particular person privateness. This encompasses the best to manage one’s private info, together with its assortment, use, and disclosure.
The information leak represents a extreme breach of this proper. This includes not simply the rapid hurt to Piper Quinn, but additionally to anybody whose knowledge was included within the alleged launch. The publicity of delicate info, corresponding to medical data, monetary particulars, or private communications, can result in discrimination, identification theft, and social stigma. Think about the Cambridge Analytica scandal, the place person knowledge was harvested with out consent and used for political functions; this incident highlights the moral failures of prioritizing revenue or affect over particular person privateness.Reputational injury is one other vital moral concern.
The discharge of private info can have devastating penalties for a person’s skilled and private life. It might result in job loss, social isolation, and injury to relationships. The framework ought to assess the potential for reputational hurt and develop methods to mitigate its influence. This will likely embrace offering assist to these affected, working to appropriate misinformation, and advocating for accountable media protection.
The potential for the info for use for blackmail or harassment should even be thought of.The moral framework also needs to consider the potential for the leak to contribute to a chilling impact on freedom of expression. If people worry that their non-public info will probably be uncovered, they could be much less more likely to categorical themselves freely, take part in public discourse, or interact in different actions that would make them weak to assault.
The framework ought to assess the potential for such a chilling impact and suggest measures to guard freedom of expression.Lastly, the framework ought to think about the broader societal influence of the leak. This contains the potential for the leak to undermine belief in establishments, corresponding to expertise firms, authorities businesses, and the media. It additionally contains the potential for the leak to normalize the observe of knowledge breaches and encourage future assaults.
The framework ought to deal with these broader societal impacts and suggest measures to forestall future incidents.
Stakeholder Evaluation of the Piper Quinn Leak
The Piper Quinn knowledge leak would influence quite a lot of stakeholders, every experiencing distinctive harms. A structured evaluation clarifies the precise penalties:
| Stakeholder | Potential Harms | Description of Hurt | Illustrative Instance |
|---|---|---|---|
| Piper Quinn | Reputational Harm, Emotional Misery, Monetary Loss | Harm to private {and professional} repute, anxiousness, melancholy, potential lack of revenue on account of broken alternatives, and the prices of coping with identification theft or authorized actions. | A celeb’s non-public medical data being leaked, leading to a lack of endorsement offers and public scrutiny. |
| People whose knowledge was leaked | Privateness Violation, Id Theft, Harassment, Discrimination | Publicity of private info resulting in unauthorized use of identification, on-line harassment, and unfair remedy based mostly on the disclosed knowledge. | Monetary info being leaked, resulting in fraudulent prices on bank cards or the opening of faux accounts. |
| Organizations Concerned (e.g., Information Storage Suppliers) | Reputational Harm, Authorized Penalties, Monetary Loss | Harm to the group’s public picture, potential fines from regulatory our bodies, and prices related to incident response, authorized charges, and lack of buyer belief. | A social media platform dealing with a large knowledge breach leading to person exodus and vital fines. |
| Basic Public | Erosion of Belief, Elevated Surveillance Considerations, Potential for Misinformation | Lack of belief in on-line safety and privateness, heightened consciousness of surveillance dangers, and the unfold of false info or propaganda based mostly on the leaked knowledge. | The discharge of manipulated or out-of-context knowledge used to sway public opinion throughout an election. |
Analyze the anticipated influence on Piper Quinn’s skilled and private life if the leak is verified
The potential verification of a leak regarding Piper Quinn in 2026 presents a multifaceted problem, able to considerably altering each her skilled trajectory and private well-being. The repercussions, if the info is confirmed as genuine, may vary from rapid profession setbacks to long-term injury to her repute and relationships. Understanding the breadth of those impacts is essential for assessing the complete scope of the scenario.
Profession Implications of a Verified Leak
The skilled sphere is especially weak to the fallout from a verified leak. Piper Quinn’s profession, no matter her occupation, would doubtless face rapid and long-term penalties. A knowledge breach of this nature, particularly if it includes delicate or confidential info, can quickly erode public belief and open the door to a large number of challenges.
- Lack of Alternatives: The leisure trade, company world, or any area that values discretion and privateness, typically prioritizes repute. A verified leak, relying on its content material, may result in the rapid rescinding of job provides, cancellation of contracts, and a normal reluctance from potential employers or collaborators. That is notably true if the leaked info reveals behaviors or info that battle with the values of firms or the expectations of the general public.
Think about the case of a outstanding celeb whose leaked private emails led to the cancellation of a profitable endorsement deal on account of perceived insensitivity.
- Public Notion and Model Harm: The courtroom of public opinion is notoriously fickle. The content material of the leak would dictate the severity of the backlash. Data perceived as damaging, whether or not true or not, may result in a decline in her model worth. This might lead to a lower in social media engagement, lack of followers, and the general erosion of her public picture. Within the digital age, a single incident can go viral, resulting in widespread scrutiny and doubtlessly irreversible injury to a fastidiously cultivated picture.
That is exemplified by the quite a few situations of public figures whose careers had been severely impacted by scandals, even when the knowledge was later confirmed to be inaccurate or taken out of context.
- Contractual Obligations and Authorized Repercussions: Contracts typically embrace clauses associated to confidentiality, morality, and model illustration. A verified leak may result in breach-of-contract lawsuits, notably if the leaked info violates these clauses. Moreover, relying on the character of the info, Piper Quinn may face authorized motion from people or organizations affected by the leak. The potential monetary burden related to authorized charges, settlements, and damages could possibly be substantial.
An analogous state of affairs will be noticed in instances the place firms confronted huge fines and litigation on account of knowledge breaches that uncovered delicate buyer info, leading to substantial losses and reputational injury.
- Impression on Future Initiatives: The leak may create challenges in securing funding for future tasks, whether or not in movie, enterprise ventures, or different areas. Traders and companions could also be hesitant to affiliate themselves with a person whose repute is perceived as tarnished. This hesitancy may result in mission delays, lowered budgets, and problem attracting expertise. The leisure trade, as an example, depends closely on investor confidence, and a scandal can instantly influence a mission’s monetary viability.
Private and Social Penalties of a Verified Leak
Past the skilled ramifications, a verified leak would invariably influence Piper Quinn’s private life. The emotional toll, pressure on relationships, and the pervasive influence on her social interactions could possibly be devastating.
- Impression on Relationships: The leak’s content material would undoubtedly pressure relationships with household, pals, and romantic companions. The revelation of delicate private info may result in emotions of betrayal, anger, and distrust. The general public scrutiny that follows may place further stress on these relationships, forcing people to navigate the fallout within the public eye. Think about the instances the place relationships crumbled following the general public disclosure of personal info, resulting in emotional misery and a breakdown in belief.
- Emotional and Psychological Misery: The emotional burden of coping with a leak of this nature could possibly be immense. The invasion of privateness, the general public humiliation, and the fixed scrutiny may result in anxiousness, melancholy, and different psychological well being challenges. The worry of judgment, the lack of management over private info, and the barrage of detrimental consideration may have a profound influence on her well-being.
That is supported by research that present the detrimental results of on-line harassment and public shaming on psychological well being.
- Social Isolation and Public Scrutiny: The aftermath of a verified leak may result in social isolation. Piper Quinn may discover herself avoiding public locations or withdrawing from social actions to keep away from undesirable consideration and judgment. The fixed media protection, social media commentary, and public hypothesis may create a hostile surroundings, making it troublesome to navigate every day life. This may be seen in quite a few instances of people who retreated from public life on account of intense media scrutiny and the stress of public opinion.
- Lengthy-Time period Psychological Results: The trauma related to a serious knowledge leak can have long-lasting psychological results. The expertise may influence her capability to belief others, kind new relationships, and preserve a way of safety. The fixed worry of additional breaches or the misuse of her info may create a persistent state of tension and vigilance. The restoration course of would doubtless require skilled assist and a big funding in rebuilding belief and privateness.
“I’m conscious of the allegations circulating on-line. Whereas I’m unable to touch upon the specifics right now, I need to guarantee everybody that I’m taking this matter very critically. I’m cooperating totally with the related authorities and am dedicated to defending my privateness and repute. I perceive that it is a troublesome time for everybody concerned, and I ask for persistence and respect as we navigate this case. I’ll present additional updates as quickly as I’m in a position. This example is extremely troublesome, and I am devastated by the influence this may occasionally have on my family members and myself. I’m consulting with authorized counsel and will probably be pursuing all accessible choices to handle this matter. I’m additionally searching for assist to deal with the emotional toll this has taken. My precedence is to maneuver ahead and guarantee my well-being.
Discover the potential for misinformation and disinformation campaigns surrounding the Piper Quinn leak
The alleged Piper Quinn leak in 2026 presents a fertile floor for the proliferation of misinformation and disinformation. Dangerous actors, motivated by varied agendas, may exploit the leaked knowledge to govern public notion, injury reputations, and even affect real-world occasions. The very nature of leaked info, typically incomplete and out of context, makes it notably weak to manipulation. This part delves into the methods these campaigns may unfold, detailing the ways employed and the potential influence on people and society.
Exploiting the Leak for Misinformation
The leaked knowledge offers quite a few avenues for spreading misinformation. That is notably regarding as a result of the general public’s belief in info sources will be simply eroded.
- Deepfakes: Refined synthetic intelligence algorithms can create lifelike movies and audio recordings of Piper Quinn, seemingly partaking in actions or making statements which might be solely fabricated. These deepfakes will be quickly disseminated throughout social media platforms, making it troublesome for the general public to discern reality from fiction. The influence of deepfakes is amplified by their capability to generate sturdy emotional responses, making them notably efficient instruments for manipulation.
Think about the 2020 deepfake of a outstanding politician used to unfold false info, which illustrates the potential for vital injury.
- Manipulated Media: Current photographs and movies of Piper Quinn will be altered to painting her in a detrimental mild or to recommend she is concerned in actions she didn’t take part in. This could contain refined modifications, corresponding to altering the context of {a photograph} or including fabricated dialogue to a video clip. The accessibility of picture and video enhancing software program makes this tactic more and more straightforward to implement and troublesome to detect.
The whispers surrounding the “piper quinn leak 2026” proceed to flow into, elevating questions on knowledge safety and privateness. These issues echo comparable anxieties in different sectors, such because the health trade. Hypothesis has additionally emerged concerning the nala fitness leak 2026 , including one other layer to the complicated panorama of digital vulnerabilities, in the end underscoring the potential influence of the “piper quinn leak 2026” on a broader scale.
For instance, a photograph of a celeb attending a charity occasion is likely to be digitally altered to make it seem they had been at a distinct, controversial location.
- Fabricated Narratives: The leaked knowledge can be utilized as a basis for setting up solely false narratives about Piper Quinn’s private {and professional} life. This might contain creating faux paperwork, emails, or social media posts that seem to originate from her or her associates. These fabricated narratives, fastidiously crafted to use current biases and prejudices, will be extremely efficient in shaping public opinion.
Think about the 2016 US presidential election, the place fabricated information tales considerably influenced voter perceptions.
Creating Disinformation Campaigns Utilizing the Leak
Disinformation campaigns, designed to intentionally mislead and deceive, may leverage the Piper Quinn leak to attain particular aims. These campaigns typically contain coordinated efforts to unfold false info throughout a number of platforms.
The anticipation surrounding the Piper Quinn leak of 2026 is constructing, with hypothesis operating rampant throughout varied on-line platforms. Whereas particulars stay scarce, some are inevitably evaluating it to different high-profile content material releases. The seek for the “finest cruella morgan onlyfans leaks” best cruella morgan onlyfans leaks can be trending, nevertheless, the main target in the end returns to the upcoming Piper Quinn materials and its potential influence.
- Goal: Harm Piper Quinn’s Popularity: The first purpose of a disinformation marketing campaign is likely to be to destroy Piper Quinn’s public picture {and professional} standing. This might contain spreading false accusations, highlighting her supposed flaws, and making a local weather of mistrust round her. The marketing campaign may goal her relationships, enterprise dealings, or private beliefs.
- Goal: Affect Public Opinion: The leak could possibly be used to form public notion of a specific subject or occasion, utilizing Piper Quinn as a focus. As an example, if Piper Quinn is perceived as an advocate for a particular trigger, the leak could possibly be used to discredit her and, by extension, the trigger she helps.
- Goal: Incite Social Division: Disinformation campaigns can be utilized to exacerbate current social divisions by concentrating on particular teams or people related to Piper Quinn. This might contain spreading hate speech, inciting violence, or selling conspiracy theories. The purpose is to create discord and instability inside society.
- Strategies:
- Social Media Bots and Trolls: Automated accounts and human-operated trolls can be utilized to amplify false narratives, harass people, and unfold disinformation throughout social media platforms. These accounts will be programmed to interact in particular actions, corresponding to liking, sharing, and commenting on posts that promote the disinformation.
- Faux Information Web sites: Web sites designed to imitate professional information sources will be created to publish fabricated tales and articles associated to the Piper Quinn leak. These web sites typically use credible-looking domains and layouts to deceive readers.
- Paid Promoting: Commercials on social media and engines like google can be utilized to advertise disinformation, reaching a wider viewers. These adverts will be focused to particular demographics or people based mostly on their on-line conduct and pursuits.
- Coordination and Cross-Promotion: Disinformation campaigns typically contain coordinated efforts throughout a number of platforms and channels. This might embrace cross-posting content material, sharing info between completely different accounts, and utilizing hashtags to amplify the attain of the disinformation.
Hypothetical Social Media Publish Instance
Think about a hypothetical social media put up that is likely to be used to unfold disinformation associated to the Piper Quinn leak. The put up may seem on a platform like X (previously Twitter).The put up would come with the next:”BREAKING: Leaked paperwork reveal Piper Quinn’s secret involvement with [fictitious organization]. These paperwork, obtained from the latest knowledge breach, present [detailed but fabricated information about Quinn’s alleged actions].
It is a clear betrayal of [Quinn’s stated values/public image]. #PiperQuinnLeak #Fact #Uncovered”The put up’s accompanying content material may function a screenshot of a fabricated doc with a watermark and official-looking logos. The doc may comprise alleged monetary transactions, emails, or assembly minutes. It will doubtless use inflammatory language to evoke sturdy emotional responses and create a way of urgency. The put up would additionally doubtless embrace a hyperlink to a web site or weblog that additional elaborates on the fabricated story, utilizing persuasive writing to provide the narrative credibility.
The web site’s design would seem skilled, utilizing components like inventory photographs and credible-sounding testimonials to boost its believability.
Look at the preventative measures that would have been applied to guard Piper Quinn’s info
The alleged leak regarding Piper Quinn in 2026 underscores the vital want for strong knowledge safety methods. Stopping such incidents requires a multifaceted strategy, combining technical safeguards, stringent protocols, and proactive private safety measures. The next sections element preventative methods that would have been applied to safeguard Piper Quinn’s delicate info, emphasizing each proactive and reactive approaches to attenuate the chance of knowledge breaches.
Safety Protocols and Practices
Piper Quinn, or her representatives, may have applied a number of safety protocols and practices to forestall the alleged leak. These measures span throughout varied domains, from technical infrastructure to private conduct, all aimed toward making a complete protection in opposition to cyber threats and unauthorized entry. A layered strategy, integrating a number of safety measures, is mostly the best technique.
- Enhanced Password Administration: Sturdy, distinctive passwords for all accounts are elementary. Using a password supervisor to generate and retailer complicated passwords is a sensible resolution. Moreover, multi-factor authentication (MFA) ought to be enabled on all accounts, together with e-mail, social media, and cloud storage companies. MFA provides an additional layer of safety by requiring a second verification technique, corresponding to a code despatched to a cellular machine, even when a password is compromised.
- Common Safety Audits and Penetration Testing: Periodic safety audits and penetration testing, carried out by unbiased cybersecurity specialists, are important. These audits determine vulnerabilities in programs and purposes earlier than malicious actors can exploit them. Penetration testing simulates real-world assaults to evaluate the effectiveness of current safety controls. These assessments ought to be carried out not less than yearly, or extra incessantly if vital modifications are made to the IT infrastructure.
- Information Encryption: Delicate knowledge, each at relaxation and in transit, ought to be encrypted. Encryption protects knowledge from unauthorized entry even when a tool is misplaced or stolen or a system is compromised. Implementing encryption throughout all units and storage options is essential.
- Safe Communication Channels: Using safe communication channels for delicate info change is vital. This contains utilizing end-to-end encrypted messaging apps, corresponding to Sign or WhatsApp, for personal conversations. Electronic mail communication also needs to be secured utilizing encryption protocols like S/MIME or PGP.
- Worker Coaching and Consciousness: Common cybersecurity coaching for all personnel, together with Piper Quinn herself, is vital. This coaching ought to cowl subjects corresponding to phishing consciousness, social engineering ways, and protected looking practices. Staff ought to be educated on methods to determine and report suspicious actions.
- Bodily Safety Measures: Bodily safety measures, corresponding to restricted entry to units and knowledge storage places, are important. This contains controlling entry to Piper Quinn’s units, making certain they’re at all times in a safe surroundings. Bodily safety breaches can typically result in knowledge theft, and you will need to take applicable precautions.
- Incident Response Plan: A complete incident response plan ought to be in place to handle any safety breaches. The plan ought to Artikel the steps to be taken within the occasion of an information leak, together with containment, investigation, notification, and restoration.
- Common Software program Updates: Retaining all software program and working programs updated is essential. Software program updates typically embrace safety patches that deal with recognized vulnerabilities. Outdated software program is a standard entry level for attackers.
Strategies for Safeguarding Private Information
Varied strategies exist for safeguarding private knowledge, every with its strengths and weaknesses. The effectiveness of those strategies is determined by the precise risk mannequin and the sensitivity of the info. A mix of strategies, tailor-made to the person’s wants, normally offers the perfect safety.
- Encryption: Encryption transforms knowledge into an unreadable format, rendering it ineffective to unauthorized people. It’s a elementary safety measure, relevant to knowledge at relaxation (saved on units) and knowledge in transit (transmitted over networks). There are numerous encryption algorithms, corresponding to AES (Superior Encryption Customary), providing completely different ranges of safety.
Encryption is a cornerstone of knowledge safety.
- Entry Controls: Implementing strict entry controls limits who can entry particular knowledge. This includes utilizing sturdy authentication strategies (passwords, MFA) and role-based entry management (RBAC), which grants entry solely to the info mandatory for a person’s job perform. This limits the influence of a breach if an account is compromised.
- Information Loss Prevention (DLP): DLP programs monitor and stop delicate knowledge from leaving a company’s management. They’ll determine and block makes an attempt to transmit confidential info by way of e-mail, USB drives, or cloud storage. DLP is especially helpful for safeguarding in opposition to insider threats and unintentional knowledge leaks.
- Information Masking and Anonymization: Information masking and anonymization strategies are used to guard delicate info by altering it whereas nonetheless sustaining its utility for evaluation or testing functions. Information masking replaces delicate knowledge with lifelike, however fictitious, values. Anonymization removes or modifies personally identifiable info (PII) to make it unattainable to determine the person.
- Cybersecurity Insurance coverage: Cybersecurity insurance coverage may help mitigate the monetary influence of an information breach. Insurance policies sometimes cowl prices related to incident response, authorized charges, and reputational injury. Whereas it doesn’t forestall a breach, it offers monetary safety.
- Common Backups: Frequently backing up knowledge is important for knowledge restoration in case of a breach, system failure, or ransomware assault. Backups ought to be saved offline or in a safe location, separate from the first knowledge storage. Testing the backups often ensures they are often restored efficiently.
These strategies, when mixed and applied successfully, considerably cut back the chance of knowledge breaches and shield delicate private info.
Cybersecurity Vulnerabilities and Mitigation Methods
A number of cybersecurity vulnerabilities may have been exploited to acquire Piper Quinn’s knowledge. Understanding these vulnerabilities and implementing applicable mitigation methods is essential for knowledge safety.
- Phishing Assaults: Phishing assaults contain tricking people into revealing delicate info, corresponding to passwords or monetary particulars. Attackers typically use misleading emails or web sites that mimic professional sources.
- Mitigation: Worker coaching on figuring out phishing makes an attempt, utilizing spam filters, and enabling MFA.
- Malware Infections: Malware, together with viruses, Trojans, and ransomware, can compromise units and steal knowledge. Malware will be launched by way of malicious downloads, contaminated e-mail attachments, or compromised web sites.
- Mitigation: Utilizing up-to-date antivirus software program, practising protected looking habits, and often backing up knowledge.
- Weak Passwords: Weak or simply guessable passwords make accounts weak to brute-force assaults or credential stuffing.
- Mitigation: Imposing sturdy password insurance policies, utilizing password managers, and enabling MFA.
- Susceptible Software program: Exploiting vulnerabilities in outdated or unpatched software program. Attackers can exploit recognized safety flaws to realize entry to programs.
- Mitigation: Retaining software program updated with the newest safety patches, often scanning for vulnerabilities, and utilizing a vulnerability administration system.
- Social Engineering: Manipulating people into revealing confidential info or performing actions that compromise safety. This could contain impersonation, pretexting, or different misleading ways.
- Mitigation: Worker coaching on recognizing social engineering ways, verifying requests, and implementing strict entry controls.
- Insider Threats: Malicious or negligent actions by people with approved entry to programs or knowledge. This could embrace staff, contractors, or third-party distributors.
- Mitigation: Implementing background checks, monitoring person exercise, and utilizing DLP programs to forestall knowledge exfiltration.
- Information Breaches at Third-Occasion Suppliers: Counting on third-party companies, corresponding to cloud storage suppliers or social media platforms, will increase the chance of knowledge breaches.
- Mitigation: Selecting respected suppliers with sturdy safety practices, reviewing their safety insurance policies, and encrypting delicate knowledge earlier than storing it with third events.
Ending Remarks
In conclusion, the piper quinn leak 2026 state of affairs underscores the complicated interaction of expertise, human conduct, and societal norms within the digital age. It is a stark reminder that knowledge safety is not only a technical problem however a multifaceted subject with profound moral and private implications. Whereas the hypothetical nature of this occasion permits for exploration, it’s essential to acknowledge that the vulnerabilities and dangers are very actual.
Vigilance, schooling, and proactive measures are important to navigating the digital panorama and safeguarding private info. The teachings discovered from this potential occasion ought to function a catalyst for a safer, accountable, and privacy-conscious future, urging a collective dedication to defending our digital selves.
Query Financial institution
What are the authorized variations between an information breach and an information leak?
A knowledge breach sometimes includes unauthorized entry to knowledge, typically by way of hacking or system compromise. A knowledge leak, alternatively, normally implies that the info was deliberately or unintentionally launched by somebody with approved entry, like an worker or a contractor. Each have critical authorized implications, however the particular prices could fluctuate relying on the circumstances.
Might insurance coverage cowl the prices related to an information leak?
Sure, relying on the kind of insurance coverage coverage. Cyber legal responsibility insurance coverage can cowl varied prices, together with authorized charges, notification bills, and credit score monitoring companies for affected people. Nevertheless, the precise protection is determined by the coverage’s phrases and situations.
How can somebody confirm the authenticity of leaked knowledge?
Verifying the authenticity of leaked knowledge is extraordinarily troublesome and sometimes unattainable. Nevertheless, specialists could search for indicators corresponding to metadata consistency, supply verification, and unbiased corroboration. Be cautious of any knowledge that seems with out clear provenance or verification from respected sources.
What position do social media platforms play within the unfold of leaked knowledge?
Social media platforms can considerably amplify the unfold of leaked knowledge, offering a fast dissemination channel for info, each correct and inaccurate. They’ll additionally turn out to be a hub for dialogue, hypothesis, and the formation of public opinion across the leak, influencing the narrative and public notion.
What are the long-term psychological well being results of being concerned in an information leak?
The long-term psychological well being results will be extreme, together with anxiousness, melancholy, PTSD, and social isolation. Victims could expertise ongoing worry, mistrust, and problem forming relationships. Skilled remedy and assist teams are sometimes mandatory to deal with the emotional and psychological trauma.